Difference between revisions of "Multi-factor authentication for Office 365"
| Line 68: | Line 68: | ||
[https://thenextweb.com/google/2019/05/23/google-data-shows-2-factor-authentication-blocks-100-of-automated-bot-hacks/ Google data shows 2-factor authentication blocks 100% of automated bot hacks - The Next Web] | [https://thenextweb.com/google/2019/05/23/google-data-shows-2-factor-authentication-blocks-100-of-automated-bot-hacks/ Google data shows 2-factor authentication blocks 100% of automated bot hacks - The Next Web] | ||
| + | |||
[https://heimdalsecurity.com/blog/start-using-two-factor-authentication/ Why You Should Start Using Two-Factor Authentication Now - Heimdal Security] | [https://heimdalsecurity.com/blog/start-using-two-factor-authentication/ Why You Should Start Using Two-Factor Authentication Now - Heimdal Security] | ||
| + | |||
[https://www.wired.com/story/two-factor-authentication-apps-authy-google-authenticator/ How to Secure Your Accounts with Better Two-Factor Authentication - Wired.com] | [https://www.wired.com/story/two-factor-authentication-apps-authy-google-authenticator/ How to Secure Your Accounts with Better Two-Factor Authentication - Wired.com] | ||
[[Category:Security]][[Category:Microsoft Office 365]] | [[Category:Security]][[Category:Microsoft Office 365]] | ||
Revision as of 15:30, 13 June 2019
About this article
This article includes the steps involved in configuring multi-factor authentication (MFA) for Microsoft Office 365. It is intended for all WSU students, faculty, and staff.
What's Office 365 Multi-Factor Authentication (MFA)?
In order to better protect you, your data, and our campus network from increasingly sophisticated phishing and other social engineering attacks, Winona State University will be implementing an Office 365 (O365) security feature this fall called Multi Factor Authentication (MFA). Once enabled, your password alone (which someone could have stolen from you) will not be enough to prove your true identity when you log into O365. In addition to your username and password, O365 will ask for more proof before it lets you in the door. Think of it as a special knock or a secret handshake. O365 will not request your special handshake every time you log in from your office or other "trusted" computers, only when it detects something has changed or your account is being used someplace new.
MFA Options
You can choose from several MFA options and can use different options in different situations, depending on what's most convenient for you. The type of handshake or knock you choose can have an impact on how and where your account can be used, so we want you to be well-informed before you decide what is best for you.
Option 1: Smartphone Notification App
This is generally the easiest option for people who have a smartphone and is presented as "Notify me through app". When the system needs additional assurance to verify your password was really entered by you, a popup is seen on your phone that asks you "Do you approve this login Y/N" All you need to do is press Y or N to confirm you expected that login and the rest is automatic. This application is easy to configure, easy to monitor and consumes very little data and battery. The upside of this option is that it makes your O365 account accessible to you wherever you bring your smartphone. If you need to access your account on your home computer, press Y on your phone. If you need to access your account from a hotel lobby kiosk, press Y on your phone. The only downside to this option is that not everyone has a smartphone or is willing to use their smartphone for anything work-related. This is why there are other options.
Option 2: Cell Phone Text
This is the next easiest way for people who either don't have a smartphone or don't want the overhead of the application to verify their identify when the need arises. The "text a code to my phone" option will simply text you a seemingly random 6-digit number that you will be prompted to enter after your password. When you enter the correct numbers it sent, the system is relatively certain it is you and not a hacker with a stolen password and will let you in. This option is again very easy to set up, requires very little configuration, and relies on only basic texting service. While it isn't quite as easy as the notification app, it does provide people with the ability to access their account while not at work or on a work laptop, which can be important to some people. While not required, leveraging a personal cellular device does provide you the most flexibility in accessing your work account when not at work.
Option 3: Smartphone Code Generating App
Similar to the 6-digit codes sent via text to your cell phone, the code generator app is a way to verify your identity, but without the data requirements of Option 1 or even the cellular text requirement of Option 2. It will work in the basement of a fallout shelter. Though not as easy as pressing Y or N, it does provide users a good option if they are frequently in a location where cellular service is poor, but they have Internet access through a different provider.
Option 4: Call My Personal Phone
This option is for anyone who wants to be able to access their O365 account from off-campus but doesn't have a smartphone or cell phone capable of receiving a text. This option works on any home phone or basic cell phone. When the system doesn't recognize you logging in, you will receive a phone call with an automated voice asking you to approve this logon attempt. If you weren't expecting this call you would obviously not approve it, but if you had just typed your password into your home computer you would press a number to finish the logon process. This isn't an ideal option for most people because it is much slower and less mobile that the others, but it can be very helpful in a pinch.
Option 5: Call My Office Phone
Just like Option 4, O365 has your university office phone number pre-populated and can call you to confirm your logon. If you forgot your cell phone at home, or dropped it in the river over the weekend, this option is a fail-safe that will allow you to get logged in when you return on Monday morning. Again, this option can be cumbersome and will not facilitate access on a home computer or anywhere that isn't within arm's reach of your work desk phone, but it does ensure that you can get your work done on your work computer when you are at work.
Option 6: University Laptop or Tablet Code Generating App
Exactly like Option 3, it is possible to install a code generator application on a university laptop or tablet that will function as extra "proof" it is you when you log in. This option may look appealing; however we don't feel it will be overly helpful for most people. After all, if you have your university laptop at home, why check your mail on your home computer? It will already be working on your laptop! However, there may be a few specific use cases for this option. Perhaps someone doesn't have a cell phone or a home phone and still really needs to use a home computer? If you are interested in this option, contact the Technical Support Center (TechSupport@winona.edu, 507-457-5240, Somsen Hall 207).
Setup Trust Account
If you see other choices you may have set something up previously. Office 365 personal or security and privacy settings contain some of this info so it may have been added previously.
1. Go to https://account.activedirectory.windowsazure.com/Proofup.aspx
2. Sign into your account and setup MFA
Our Recommendations
- Provided you have a smart phone, we highly recommend using the Notify Me through app using the Microsoft Authenticator app as your #1 choice; followed by a backup text. This notification process makes it super easy when your account is finally tripped.
- A regular cell phone without smart capabilities use text
- If no cell phone your options are to use your office phone or use verification code from app on a university laptop.
Setup Process
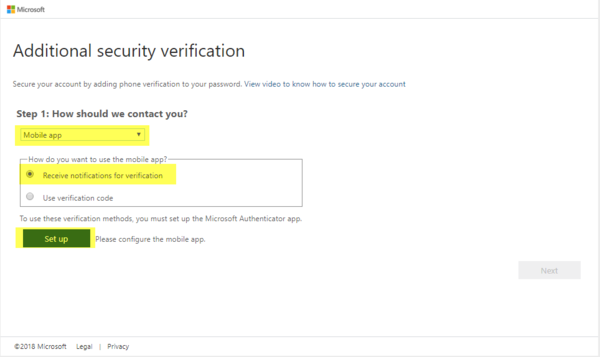
- Click on Setup
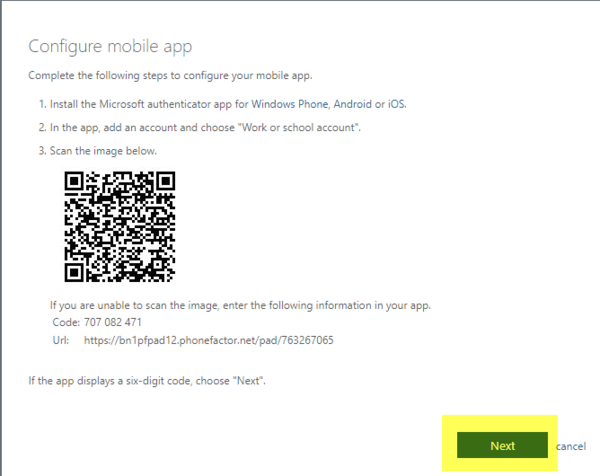
- On the next screen read through the instructions, install the app and click on Next
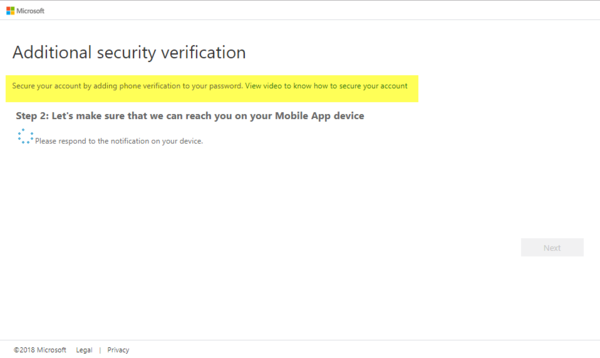
- A message will be sent to you phone
- When you get the verification message click on Approve
Activation
- Activation consists of scheduling your account to have Multifactor
- You will get a popup - Within an hour you will need to validate your account
- Type in your StarID password once and click approve (or enter text option)
More Info
Google data shows 2-factor authentication blocks 100% of automated bot hacks - The Next Web
Why You Should Start Using Two-Factor Authentication Now - Heimdal Security
How to Secure Your Accounts with Better Two-Factor Authentication - Wired.com